Source: www.darkreading.com
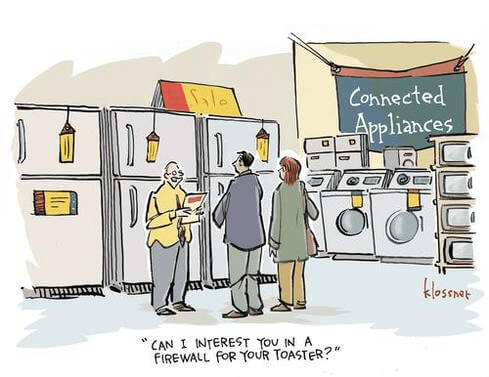
The ease with which hacks can be performed in today's complex IoT environment is nothing short of alarming given its ramifications for companies that deploy the technology. Some security challenges in the context of IoT include: Lack of security implementation during development: Since the boom started, a lot of IoT products have flooded the market, some of them very competitive. To cite an example, a product by a branded company might cost $100 in the market while its replica from a lesser-known company might be available for $10. At first blush, the two products may not be different. But look closer—the cheaper one may not have the latest/stable software or hard passwords for panel login. Cheap hardware that does not support security implementation: Most of the time, during development, developers choose a “set-and-forget-approach” to devices. To keep the price at bay, manufacturers rely on cheap hardware that does not go the extra mile in terms of security. With such devices in the IoT ecosystem, handling security becomes tough. Lack of industry standards: While many IoT security frameworks exist, there is no single agreed-upon framework. Most big companies create a model of their own while smaller industries follow proprietary-incompatible standards. This lack of standardization makes it difficult to secure systems. With OWASP IoT Top 10 draft around the corner, some of the security issues in IoT could be addressed if developers put in the effort.How to Protect Systems and Devices for IoT Security
Prevention is better than cure approach is the best, just as in every other security implementation—that is, take care of security right from the start. The operators of IoT devices need to consider their systems just like every other network-connected computer and keep their systems up to date, prevent malware, as well as audit and protect the infrastructure.- Apply threat modeling and integrate security into the development phase
- Ensure API security for connect back devices
- Ensure cryptographic strength for connections and data transport
- Ensure network and infrastructure security at deployment
- Provide software updates and patch devices at the first hint of a known threat
- Provide proper guidelines to tech support team and customers
- For critical deployment, rely on technically skilled team
- Provide passwords and debug systems that are not easily accessible
- Identify the bogie that belongs to the fleet

