Some smart guy once said the devil is in the details, and it is the details we're getting down to in this post, the last in our series on Blockchain Technology & Bitcoin Cryptocurrency.
We shall go through the following:
- What a Bitcoin transaction looks like
- Scripting languages used
- Data structure
What Does a Bitcoin Transaction Look Like?
Bitcoin follows the transaction-based ledger model, which keeps track of every transaction. To verify the authenticity of a transaction requires only a single traversal.
For the sake of simplicity, let’s consider a transaction as a set of inputs, outputs, and a unique identifier. The input section of a transaction specifies the source of the coins involved in the transaction.
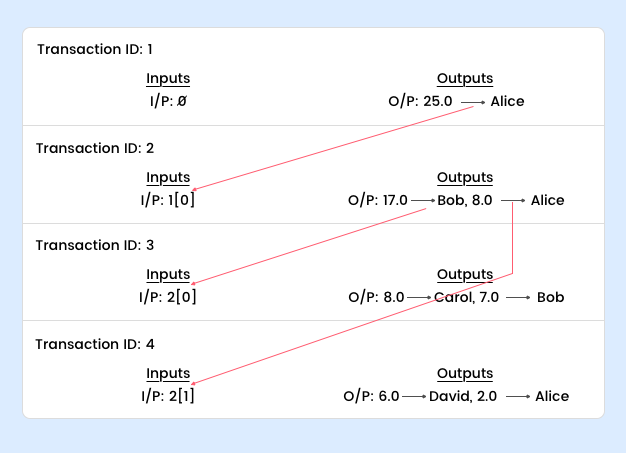 Transaction 1 is a “create coin transaction” and the recipient is Alice. When Alice wants to send some of her coins to Bob, she has to explicitly refer to the transaction where she was the recipient of those coins. Transaction 2 has the output index 0 from Transaction 1.
If you look at Transaction 2 closely, you would notice that Alice had to send the rest of the coins to herself. This is due to the design of Bitcoin—you need to completely consume the output of the previous transaction. Spending just a few coins from Transaction 1 is not possible; the rest needs to be sent back to oneself. This is called “change address.” You can group together transactions that have the same recipient, that is, you can make a joint payment.
Now that you’ve seen what a transaction looks like, let's dig a little deeper:
A transaction consists of three parts:
Transaction 1 is a “create coin transaction” and the recipient is Alice. When Alice wants to send some of her coins to Bob, she has to explicitly refer to the transaction where she was the recipient of those coins. Transaction 2 has the output index 0 from Transaction 1.
If you look at Transaction 2 closely, you would notice that Alice had to send the rest of the coins to herself. This is due to the design of Bitcoin—you need to completely consume the output of the previous transaction. Spending just a few coins from Transaction 1 is not possible; the rest needs to be sent back to oneself. This is called “change address.” You can group together transactions that have the same recipient, that is, you can make a joint payment.
Now that you’ve seen what a transaction looks like, let's dig a little deeper:
A transaction consists of three parts:
- Metadata
- A series of inputs
- A series of outputs
The metadata holds data such as the size of the transaction, the number of inputs, the number of outputs, and the hash of the entire transaction (this will serve as a unique ID for the transaction).
 The inputs specify the source of the coins used in the transaction. It also contains an index and a signature. The index denotes the output of the transaction, which a sender uses as an input. The signature verifies the sender’s claim on those coins. The output includes the value and the recipient address (the public key to which the coin goes). These addresses are not actual addresses but Bitcoin scripts.
The inputs specify the source of the coins used in the transaction. It also contains an index and a signature. The index denotes the output of the transaction, which a sender uses as an input. The signature verifies the sender’s claim on those coins. The output includes the value and the recipient address (the public key to which the coin goes). These addresses are not actual addresses but Bitcoin scripts.
What Are Bitcoin Scripts?
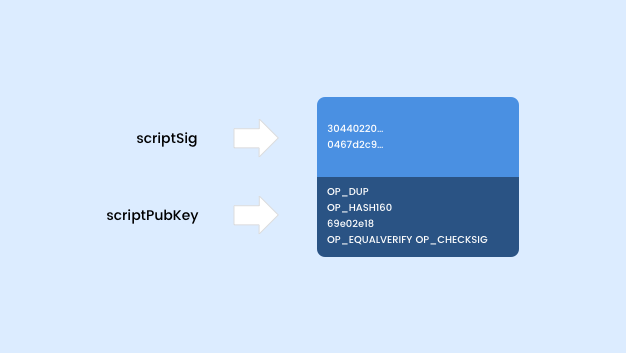
The best way to explain Bitcoin scripts would be by means of an example. Let’s look at the two most commonly used scripts in Bitcoin: scriptSig and scriptPubKey.
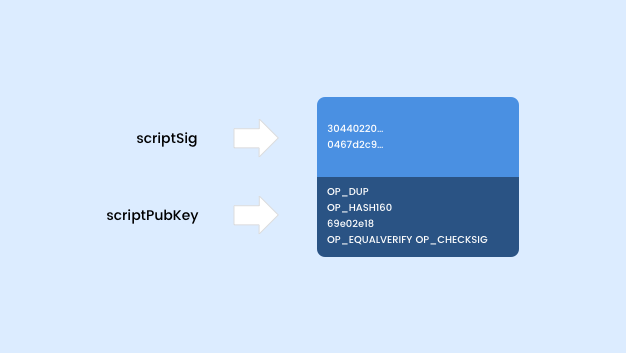 To validate a transaction, the two scripts are concatenated and executed. If they execute successfully without any errors, the transaction is considered to be a valid transaction.
To validate a transaction, the two scripts are concatenated and executed. If they execute successfully without any errors, the transaction is considered to be a valid transaction.
Bitcoin Scripting Language
The Bitcoin scripting language was inspired by Forth, a stack-based programming language. Hence, many of the features such as variables, loops, and so on are not available. But it's not necessary to learn the language to understand how the system works (so cheer up!).
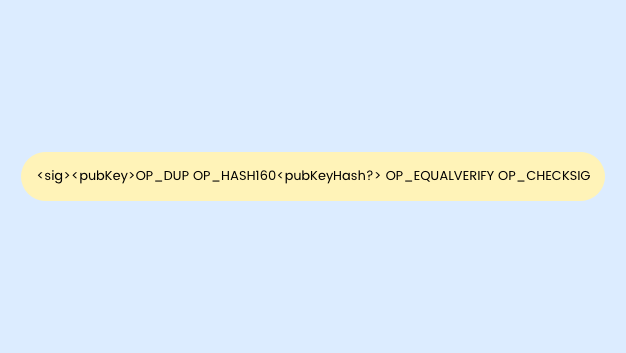
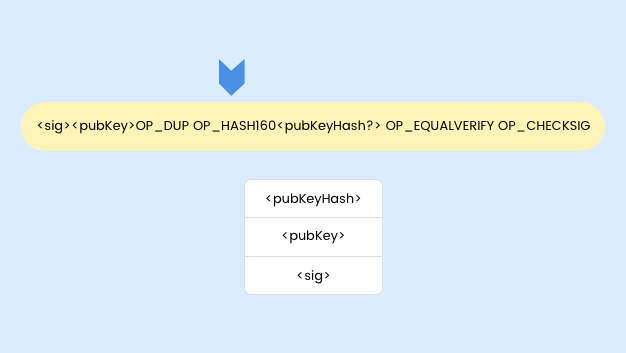
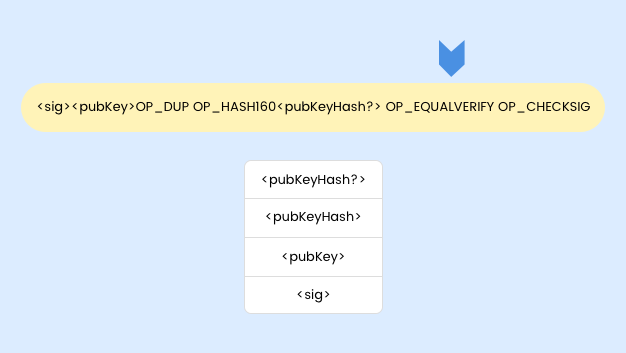
The first two instructions in the scriptSig are data instructions: the signature and public key of the sender. When data instructions are encountered, they get pushed onto the stack. Similarly, when an operation is encountered, the top of the stack gets popped, the operation is carried out, and the result is pushed back onto the stack. The main design goal of Bitcoin scripting language is to support sophisticated cryptography.
 In the above example, a sender tries to redeem a coin obtained from the previous transaction. The input address is derived from the previous transaction.
In the above example, a sender tries to redeem a coin obtained from the previous transaction. The input address is derived from the previous transaction.
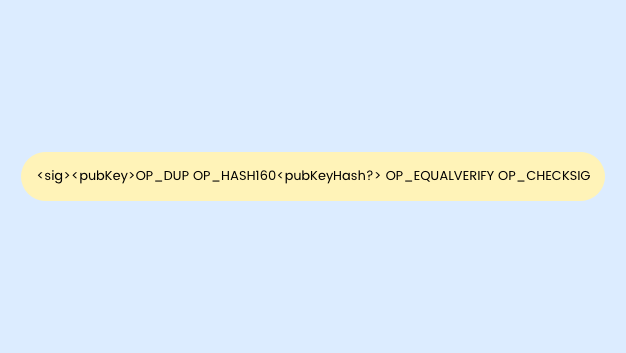
Bitcoin Script Execution
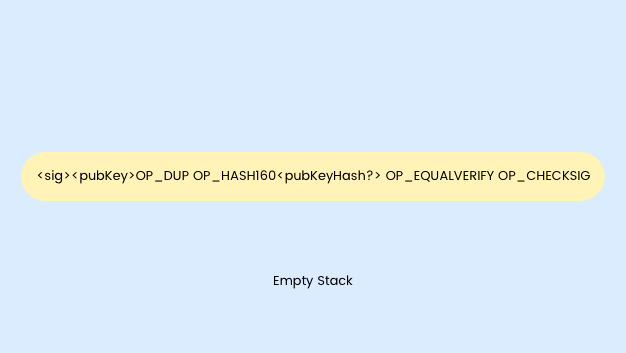
The execution of a Bitcoin script is illustrated below.
STEP 1
STEP 2
STEP 3
 The instruction OP_DUP will pop the value at the top of stack, duplicate the value, and write back two copies onto the stack. Thus we have two copies of <pubKey> in the stack.
The instruction OP_DUP will pop the value at the top of stack, duplicate the value, and write back two copies onto the stack. Thus we have two copies of <pubKey> in the stack.
STEP 4
 The HASH160 instruction takes the value at the top of the stack and computes its cryptographic hash. Thus the top of the stack is the hash of the public key: <pubKeyHash>.
The HASH160 instruction takes the value at the top of the stack and computes its cryptographic hash. Thus the top of the stack is the hash of the public key: <pubKeyHash>.
STEP 5
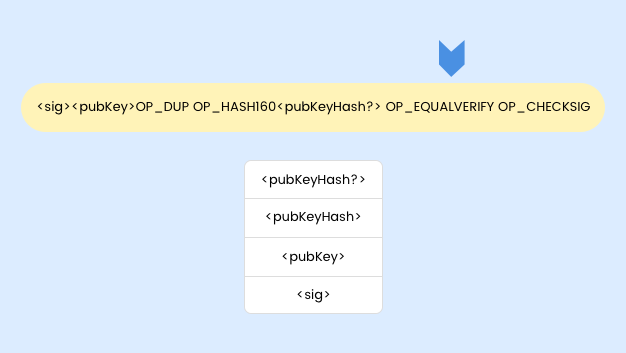 The output address of the transaction <pubKeyHash?> from which the sender received the coins is pushed onto the stack. The OP_EQUALVERIFY instruction checks if the value at the top of the stack and the one below are equal. If they aren’t, an error is shown and the script is not executed.
The output address of the transaction <pubKeyHash?> from which the sender received the coins is pushed onto the stack. The OP_EQUALVERIFY instruction checks if the value at the top of the stack and the one below are equal. If they aren’t, an error is shown and the script is not executed.
STEP 6
 Finally, we have only two values in the stack—the public key and the signature. The public key has already been verified in the previous step. We can easily verify the authenticity of the signature using the CHECKSIG instruction.
What we have witnessed is the beauty of the Bitcoin scripting language: minimal but efficient. There is no reliance on external libraries for its execution.
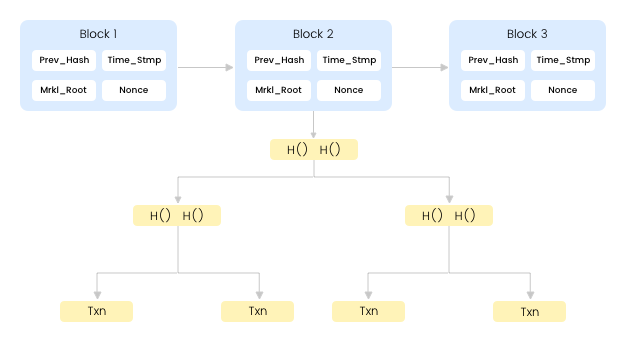
Why do we need blockchains? Why not transaction chains? Imagine the amount of work (of course, the CPU/GPU works for them) the nodes would have had to put in to find the nonce for each transaction. It is also easier for the participating nodes to verify the validity of a block rather than the validity of each transaction. Block traversal is faster than transaction traversal. Thus blocks make the life of participating nodes much easier.
Finally, we have only two values in the stack—the public key and the signature. The public key has already been verified in the previous step. We can easily verify the authenticity of the signature using the CHECKSIG instruction.
What we have witnessed is the beauty of the Bitcoin scripting language: minimal but efficient. There is no reliance on external libraries for its execution.
Why do we need blockchains? Why not transaction chains? Imagine the amount of work (of course, the CPU/GPU works for them) the nodes would have had to put in to find the nonce for each transaction. It is also easier for the participating nodes to verify the validity of a block rather than the validity of each transaction. Block traversal is faster than transaction traversal. Thus blocks make the life of participating nodes much easier.
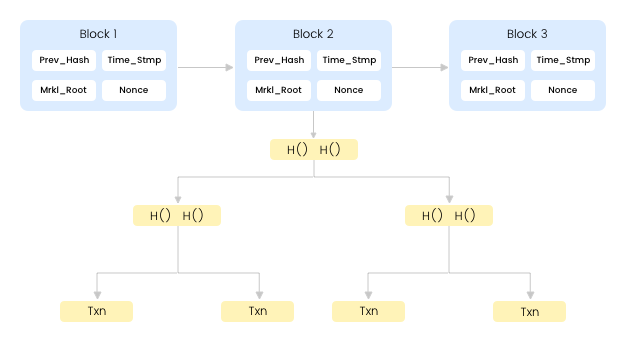
What Does a Blockchain Data Structure Look Like?
The blockchain is a combination of two hash-based data structures. We have a block header, a pointer to a transaction, a pointer to the previous transaction (hash pointer) and, finally, we have the tree of all the transactions in each block called Merkle Tree.
 Let's take up a Bitcoin block for closer inspection.
Let's take up a Bitcoin block for closer inspection.
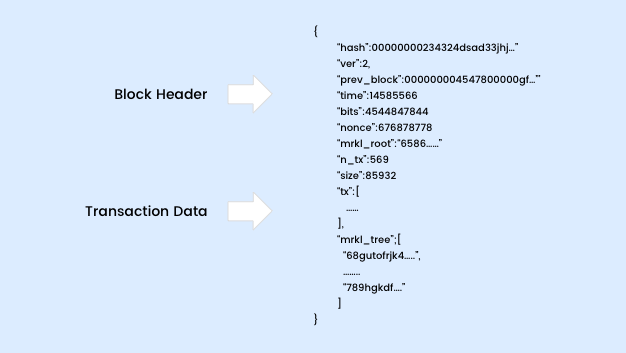 We have a block header that holds the metadata of that block and the transaction data that holds the list of transactions.
We have a block header that holds the metadata of that block and the transaction data that holds the list of transactions.
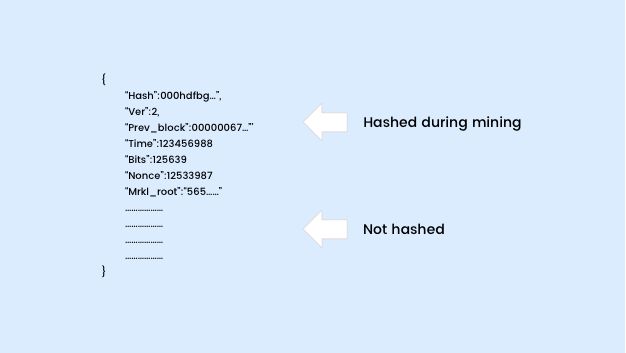 The Bitcoin block header holds the hash puzzle solution and the related information. The hash denotes the hash of block, the prev_block denotes the hash of the previous block, the nonce refers to the random number to be found, and the mrkl_root denotes the root of Merkle Tree for that block.
The Bitcoin block header holds the hash puzzle solution and the related information. The hash denotes the hash of block, the prev_block denotes the hash of the previous block, the nonce refers to the random number to be found, and the mrkl_root denotes the root of Merkle Tree for that block.
How Do We Join the Bitcoin Network?
It is quite easy to join the Bitcoin network, but you must satisfy a prerequisite. You have to know the address of at least one node before joining the network. That node is referred to as the seed node.
[caption id="attachment_17601" align="aligncenter" width="626"]
How a new node joins the Bitcoin network.[/caption]
We request the seed node to send the addresses of all the nodes it knows. Then we request the same from those nodes. This continues till we connect to a set of random nodes in the network. There is an inherent security feature in the network. Whenever a node receives two transactions that seem to spend the same coin, the first transaction is accepted and the second one is rejected.
[caption id="attachment_17596" align="aligncenter" width="600"]
Transaction propagation in Bitcoin[/caption]
Conclusion
We hope your journey through our posts on Blockchain Technology and Bitcoin Cryptocurrency was an easy one. Drop us a line, if you are keen on knowing more or would like to discuss any specific implementation.
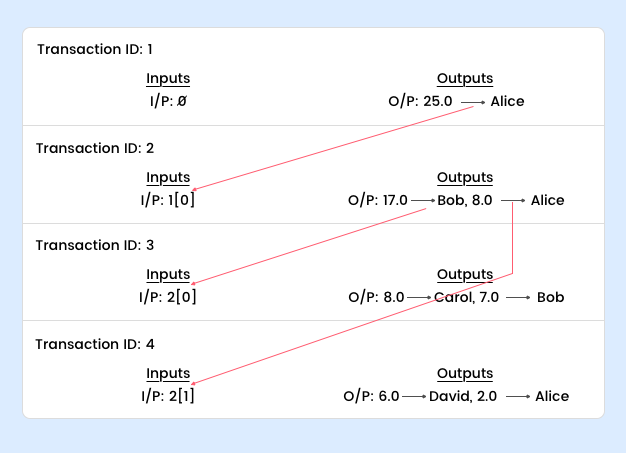 Transaction 1 is a “create coin transaction” and the recipient is Alice. When Alice wants to send some of her coins to Bob, she has to explicitly refer to the transaction where she was the recipient of those coins. Transaction 2 has the output index 0 from Transaction 1.
If you look at Transaction 2 closely, you would notice that Alice had to send the rest of the coins to herself. This is due to the design of Bitcoin—you need to completely consume the output of the previous transaction. Spending just a few coins from Transaction 1 is not possible; the rest needs to be sent back to oneself. This is called “change address.” You can group together transactions that have the same recipient, that is, you can make a joint payment.
Now that you’ve seen what a transaction looks like, let's dig a little deeper:
A transaction consists of three parts:
Transaction 1 is a “create coin transaction” and the recipient is Alice. When Alice wants to send some of her coins to Bob, she has to explicitly refer to the transaction where she was the recipient of those coins. Transaction 2 has the output index 0 from Transaction 1.
If you look at Transaction 2 closely, you would notice that Alice had to send the rest of the coins to herself. This is due to the design of Bitcoin—you need to completely consume the output of the previous transaction. Spending just a few coins from Transaction 1 is not possible; the rest needs to be sent back to oneself. This is called “change address.” You can group together transactions that have the same recipient, that is, you can make a joint payment.
Now that you’ve seen what a transaction looks like, let's dig a little deeper:
A transaction consists of three parts:
 The inputs specify the source of the coins used in the transaction. It also contains an index and a signature. The index denotes the output of the transaction, which a sender uses as an input. The signature verifies the sender’s claim on those coins. The output includes the value and the recipient address (the public key to which the coin goes). These addresses are not actual addresses but Bitcoin scripts.
The inputs specify the source of the coins used in the transaction. It also contains an index and a signature. The index denotes the output of the transaction, which a sender uses as an input. The signature verifies the sender’s claim on those coins. The output includes the value and the recipient address (the public key to which the coin goes). These addresses are not actual addresses but Bitcoin scripts.
 To validate a transaction, the two scripts are concatenated and executed. If they execute successfully without any errors, the transaction is considered to be a valid transaction.
To validate a transaction, the two scripts are concatenated and executed. If they execute successfully without any errors, the transaction is considered to be a valid transaction.
 In the above example, a sender tries to redeem a coin obtained from the previous transaction. The input address is derived from the previous transaction.
In the above example, a sender tries to redeem a coin obtained from the previous transaction. The input address is derived from the previous transaction.
 STEP 2
STEP 2
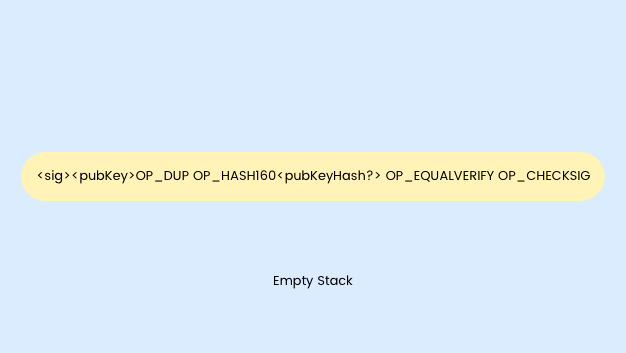 STEP 3
STEP 3
 The instruction OP_DUP will pop the value at the top of stack, duplicate the value, and write back two copies onto the stack. Thus we have two copies of <pubKey> in the stack.
STEP 4
The instruction OP_DUP will pop the value at the top of stack, duplicate the value, and write back two copies onto the stack. Thus we have two copies of <pubKey> in the stack.
STEP 4
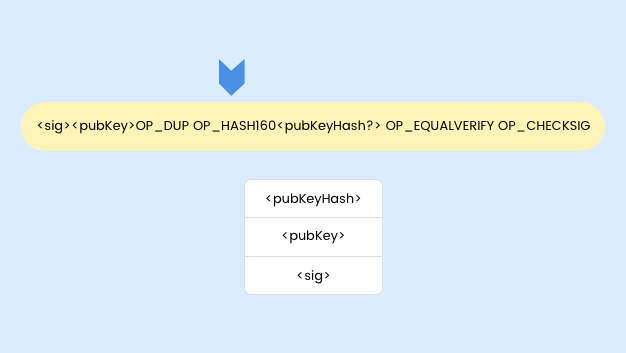 The HASH160 instruction takes the value at the top of the stack and computes its cryptographic hash. Thus the top of the stack is the hash of the public key: <pubKeyHash>.
STEP 5
The HASH160 instruction takes the value at the top of the stack and computes its cryptographic hash. Thus the top of the stack is the hash of the public key: <pubKeyHash>.
STEP 5
 The output address of the transaction <pubKeyHash?> from which the sender received the coins is pushed onto the stack. The OP_EQUALVERIFY instruction checks if the value at the top of the stack and the one below are equal. If they aren’t, an error is shown and the script is not executed.
STEP 6
The output address of the transaction <pubKeyHash?> from which the sender received the coins is pushed onto the stack. The OP_EQUALVERIFY instruction checks if the value at the top of the stack and the one below are equal. If they aren’t, an error is shown and the script is not executed.
STEP 6
 Finally, we have only two values in the stack—the public key and the signature. The public key has already been verified in the previous step. We can easily verify the authenticity of the signature using the CHECKSIG instruction.
What we have witnessed is the beauty of the Bitcoin scripting language: minimal but efficient. There is no reliance on external libraries for its execution.
Why do we need blockchains? Why not transaction chains? Imagine the amount of work (of course, the CPU/GPU works for them) the nodes would have had to put in to find the nonce for each transaction. It is also easier for the participating nodes to verify the validity of a block rather than the validity of each transaction. Block traversal is faster than transaction traversal. Thus blocks make the life of participating nodes much easier.
Finally, we have only two values in the stack—the public key and the signature. The public key has already been verified in the previous step. We can easily verify the authenticity of the signature using the CHECKSIG instruction.
What we have witnessed is the beauty of the Bitcoin scripting language: minimal but efficient. There is no reliance on external libraries for its execution.
Why do we need blockchains? Why not transaction chains? Imagine the amount of work (of course, the CPU/GPU works for them) the nodes would have had to put in to find the nonce for each transaction. It is also easier for the participating nodes to verify the validity of a block rather than the validity of each transaction. Block traversal is faster than transaction traversal. Thus blocks make the life of participating nodes much easier.
 Let's take up a Bitcoin block for closer inspection.
Let's take up a Bitcoin block for closer inspection.
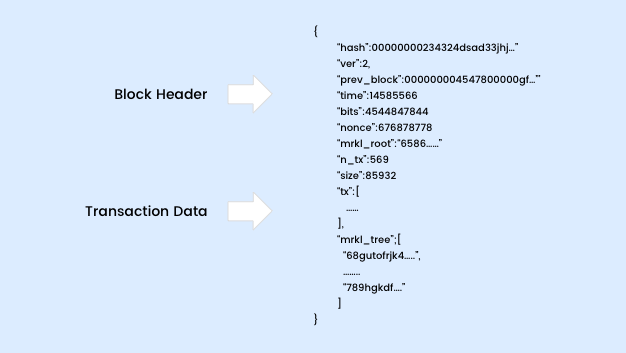 We have a block header that holds the metadata of that block and the transaction data that holds the list of transactions.
We have a block header that holds the metadata of that block and the transaction data that holds the list of transactions.
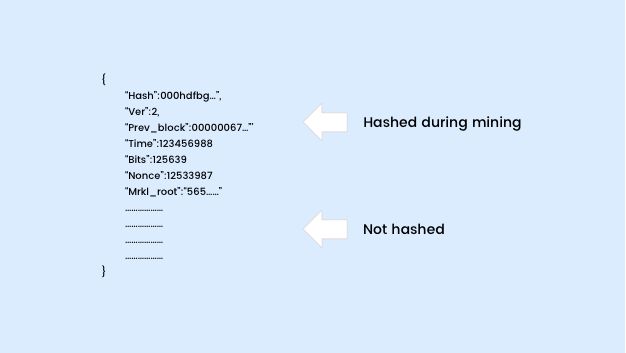 The Bitcoin block header holds the hash puzzle solution and the related information. The hash denotes the hash of block, the prev_block denotes the hash of the previous block, the nonce refers to the random number to be found, and the mrkl_root denotes the root of Merkle Tree for that block.
The Bitcoin block header holds the hash puzzle solution and the related information. The hash denotes the hash of block, the prev_block denotes the hash of the previous block, the nonce refers to the random number to be found, and the mrkl_root denotes the root of Merkle Tree for that block.
 How a new node joins the Bitcoin network.[/caption]
We request the seed node to send the addresses of all the nodes it knows. Then we request the same from those nodes. This continues till we connect to a set of random nodes in the network. There is an inherent security feature in the network. Whenever a node receives two transactions that seem to spend the same coin, the first transaction is accepted and the second one is rejected.
[caption id="attachment_17596" align="aligncenter" width="600"]
How a new node joins the Bitcoin network.[/caption]
We request the seed node to send the addresses of all the nodes it knows. Then we request the same from those nodes. This continues till we connect to a set of random nodes in the network. There is an inherent security feature in the network. Whenever a node receives two transactions that seem to spend the same coin, the first transaction is accepted and the second one is rejected.
[caption id="attachment_17596" align="aligncenter" width="600"] Transaction propagation in Bitcoin[/caption]
Transaction propagation in Bitcoin[/caption]

